In the last number of the german edition of PC PRAXIS ( edition 4 – 2010 ) we are offering the ID Disk Protector for free! The DVD included has an installer of ID Disk Protector which will fully work for 2 years. A complete review of the application with screenshots and explanations are included in the magazine.
ID Disk Protector main features:
– Protects your disk and its partitions
– Offers boot protection
– Provides a launching and operating password
– Keeps private the enable/disable of your disk
– Blocks any operations on the hardware level
Here are bellow some quotes from the PC Praxis review:
Mit dem ID Disk Protector lassen sich einzelne Laufwerke mit wenigen Klicks vor allzu neugierigen Blicken schützen. So haben Unbefugte keine Chance, an Ihre sensibilen Daten zu gelangen, und selbst wenn Ihr Notebook gestohlen werden sollte, hat der Dieb schlechte Aussichten.
….
Wer auf seinem Rechner sensible Daten aubewahrt, möchte auf keinen Fall, dass diese unbefugten Dritten un die Hände fallen. Mit dem ID Disk Protector erhalten Sie ein Tool, mit dem sich Daten auf einzelnen Laufwerken mit wenig Aufwand sicher schützen lassen.
 The
The  The statistics from january 2009 comming from
The statistics from january 2009 comming from 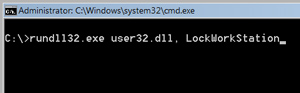
 You can use Group Policies to
You can use Group Policies to